A year ago I decided to make career move. I would be leaving a company with years of existence and going to a start-up. This brought a lot of angst and plenty of heartburn, but I decided to do it. A year later, I couldn’t be more proud of my decision. We have growing pains as all start-ups do, but I truly believe my contributions are having an impact on our future. It is difficult to branch out and expand my MVP status, but I am where I belong right now. I just got back from the 2016 MVP Summit and had to work more than I have ever had to. But working side by side with Scott Forsyth has been worth every minute of anguish I have felt. We did get to meet with the IIS team this year. I am also going to be working on a book. That is new ground for me. I have been to Denmark and worked more hours than I have in years before, but I am challenged and respected and needed in a way that I never have been. I do still work actively on the CI Security Benchmark for IIS and also speak at User Group meetings when I can. Here is to a very productive 2017 year (5th MVP year) and a profitable Dynamicweb NA venture. We can do this. ![]()
Tag: IIS
IIS WordPress implementation
This past weekend I noticed a tweet cross my feed about the security end of life for php v5.4. This happens on September 14, 2015. Thankfully I noticed this since this blog is running on WordPress and was using php v5.4. I decided it was finally time to upgrade the version of php that my sites are using.
I logged in and launched WPI and searched for php. I found that php 5.5 is already installed on my system and that php 5.6 was available for installation. I went ahead and installed php 5.6. Figured if I was going to make the update, I would go to the latest version. After installation, I changed my php version using PHP Manager, and ran the phpinfo() page. Unlike my php v5.3 and v5/4 implementations, an error page was returned. Specifically a 500.0 error:
ERROR:
C:Program Files (x86)PHPv5.6php-cgi.exe – The FastCGI process exited unexpectedly
Error code: The extended attributes are inconsistent.
(0xff)
I started off using Process Monitor from SysInternals to ensure that the root cause wasn’t an NTFS access issue. The worker process could successfully access php-cgi.exe and no errors were logged.
After doing some Googling, I came across a page that mentioned running the php.exe directly to see if any error messages were returned. Every time I tried to run php.exe from a command line, I got a CLI crash. I finally decided to simply double click the php.exe file to launch it. This provided enough information related to the problem for me to effectively research the issue. php was returning an error:
Faulting application name: php.exe, version: 5.6.0.0, time stamp: 0x53fe2967
Faulting module name: MSVCR110.dll, version: 6.3.9600.17936, time stamp: 0x55a68dd1
I was then able to narrow my search to MSVCR110.dll and found the following forums.iis.net post that resolved the issue for me.
I hope you find this post useful and it saves you some downtime on your sites.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and IT Infrastructure Specialist at Sherweb.
Setting up Web Deploy on Azure VMs
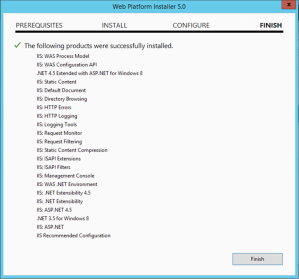
For starters, I will provide instructions on how to install IIS in case that hasn’t already been done. An easy starting point for enabling the IIS Role and additional features is to use the Web Platform Installer. After you have installed this application, follow these steps:
1. Run Web Platform Installer and search for IIS Recommended.
2. Click Add to select IIS Recommended Configuration to be installed.
3. Search for IIS: ASP.
4. Click Add on the IIS: ASP.NET 4.5 option.
5. Click Install at the bottom of the window and then click I Accept to begin the installation procedure.
This process enables the IIS Role, applies the recommended feature configuration and enables .Net 4.5. Installing these features will configure IIS correctly to serve ASP.Net websites and applications. Any additional IIS features that are required will need to be installed. For reference, here are the features that are installed using this method:
There are a few things to remember when deploying Web Deploy. More than just Web Deploy needs to be installed/configured. The IIS Management Service is used to configure remote connections to the IIS instance as well as who is authorized to connect. This can be installed either via WPI or Roles and Features with-in Server Manager itself. For this demonstration, I will use WPI to install the remaining applications. After launching WPI, search for Management and choose Add for the IIS: Management Service and then repeat for Web Deploy. Click Install. The following screen shows the selected applications ready for installation.

Click I Accept to complete the installation of the features and all dependencies.
Once the installation has completed, there will be new features added to IIS Manager. Open IIS Manager to configured the Management Service. Double click on the Management Service icon to begin.
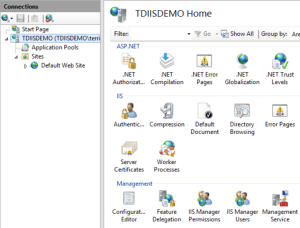
Once the feature configuration page is open, there are a few settings that needs to be updated. If the service is running, you can not make updates to the settings. Click Stop in the Actions pane if this is the case. To begin with, check the Enable remote connections setting. Rather than having to maintain IIS Manager users, I choose Windows credentials only. Notice the Enable failed request tracking option below the log setting. In the event of issues using Web Deploy, you can enable this setting to gather additional information. For additional security, you can also set IP Address Restrictions. You can restrict access to specific IP addresses by changing the Access for unspecified clients to Deny. After doing that, add an Allow entry for any IP Addresses that should be allowed to connect.
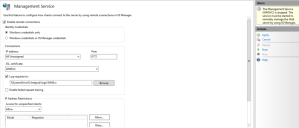
Click Apply to save the settings and then Start to start the Management Service. Minimize or close IIS Manager.
To ensure that the server is now listening on port 8172, open a command prompt and run netstat –aon | findstr :8172. You should see at least the following response. You could see others depending on your server configuration. If you do not get any response, check services and ensure that the Web Management Service is running. If it is running, check the above steps and ensure that everything is configured correctly.
![]()
We will now check the Windows Firewall to ensure that the rule for Web Management Service (HTTP Traffic-In) is enabled. This rule is created when the Web Management Service is installed.
![]()
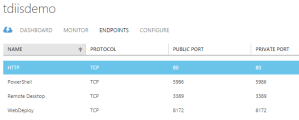
The last thing that will need to be configured is the endpoint for your Azure VM. Login to the Azure portal and navigate to your Virtual Machine endpoints. This is done differently depending on if you are using the classic portal (manage.windowsazure.com) or the new portal (portal.azure.com). Once you have located the Endpoints configuration screen for your VM, add an entry for Web Deploy for port 8172.
You are now ready to connect using Visual Studio and deploy your website or application.
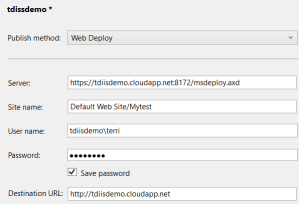
For reference, here is what a deployment configuration within Visual Studio looks like.
These steps can be followed for configuration of Web Deploy for other providers such as SherWeb’s Performance Cloud as well.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and IT Infrastructure Specialist at Sherweb.
Managing SSL Bindings with PowerShell
I recently wrote a blog post for the Hey, Scripting Guy! blog related to Updating SSL Bindings. This is a process that is time consuming and tedious when working with server farms. By automating this process with PowerShell, the manual importing of the certificates and updating the bindings can be done programmatically. Until you upgrade your IIS Servers to IIS 8 and can use the Centralized Certificate Store, this is the next best thing. Jump on over and take a look.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and IT Infrastructure Specialist at OrcsWeb, a Sherweb Company that offers managed hosting solutions
Website Encryption
I was asked a curious question the other day related to the number of websites that have SSL certificates installed. After thinking about it, big companies have SSL but most personal websites don’t. Based on my own feelings, the reason things are this way is due to the upfront and yearly costs of SSL certificates as well as not realizing the benefits of encrypting your website content.
During this discussion, a friend told me about the Let’s Encrypt project. This is an exciting new FREE Certificate Authority that will be arriving in the Summer of 2015.
Let’s Encrypt will not be for everyone. There will still be needs for the Extended Validation, wildcard, and multiple –domain certificates that are provided by Certificate Authorities such as VeriSign and GoDaddy to name a few.
The current application only supports apache but IIS is in the works. A small piece of management software is installed on the server that handles everything from proving control of the website, to requesting the certificate and installing it on the site. It also tracks certificate expiration dates ,handles auto renewal of the certificate and provides the ability to revoke the certificate if needed.
Since there is not a Windows/IIS version currently available, I do not have hands on experience with it. I am definitely looking forward to taking it for a test drive once it is available to see how it handles multiple websites on the same machine, host header sites, or even servers that have SNI and CCS installed.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and a Cloud Administrator at OrcsWeb, a hosted server company providing managed hosting solutions
HTTP/2–Through the looking glass
One of the things discussed at the MVP Summit this year was HTTP/2. The IIS group had a great session related to this upcoming protocol. Since this is being worked on across multiple companies to develop the new standard, we are able to blog about certain aspects of the protocol. The community is asking that people take an early look at the protocol. Test your applications. Try to find breaking changes so they can be addressed early in the process.
The Internet Engineering Task Force (IETF) works to produce high quality technical documents. The draft document for HTTP/2 is a great resource to gather additional information related to this undertaking.
The Windows 10 Technical Preview supports HTTP/2 on the client and server side. I decided to spin up a cloud server on my Azure account to take this for a spin. To begin with, there are a few things required in order to test. The Web Server role has to be enabled. HTTP/2 also only works over the TLS cryptographic protocol so an SSL certificate has to be bound to the testing website. I did not have to complete any of the additional steps in this blog post to ensure that HTTP/2 was enabled. Depending on the version of Technical Preview that you are using, you may need to set the registry key.
Since I want to take a look at all aspects of IIS on this version of Windows, I broke my cardinal rule of ‘Never enable all IIS Features’. The quick way to perform the install is by using PowerShell. I ran the command Add-WindowsFeature –IncludeAllSubFeature –IncludeManagementTools from Windows PowerShell. Once the installation completed, I launched IIS Manager so that I could bind an SSL certificate to the Default Web Site.
Once this was done, I opened Internet Explorer. I then pressed the F12 key to open the F12 Developer Tools so I could watch the network traffic. In the below screenshot, you can see the icon for Network. Click that icon and then click the Green start arrow. This will allow you to see the protocol that is being used between the client and the server.
Now that I had everything setup and ready to go, I navigated to https://localhost. The default IIS page is loaded over TLS and the network trace shows the protocol is HTTP2.
This is a quick way to verify that HTTP/2 is the negotiated protocol between the client and the server.
If you are interested in following the progress of the development of this protocol, here is a list of URLs that provide additional information and testing capabilities.
http://status.modern.ie
https://github.com/http2/http2-spec/wiki/implementations
https://h2duo.coudapp.net
http://blogs.msdn.com/b/ie/archive/2014/10/08/http-2-the-long-awaited-sequel.aspx
https://msopentech.com/opentech-projects/http2-0/
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and a Cloud Administrator at OrcsWeb, a hosted server company providing managed hosting solutions
Microsoft MVP Renewal
Last year on July 1st, I was anxiously waiting to hear if I had been awarded my first Microsoft MVP award for ASP.Net/IIS. Fast forward a year, and here I was waiting again to see if the ‘Congratulations 2014 Microsoft MVP!’ email was received. The MVP Award is for the previous year of community work in which you participated. For me, this included providing assistance via forums.iis.net, actively working with the Center for Internet Security on IIS related security benchmarks, doing my first speaking engagement for the Dallas asp.net User Group (thanks for the invitation Toi Wright – we’ll have to do it again), technical reviewer for a Microsoft IIS Administration training class, and blogging on my personal blog site and my company’s blog sites. I have been fairly active in the community but also know people that have been nominated that did not receive the award. I am pleased to announce that I have again received the award.
Once again, thank you Microsoft for the Award and I look forward to the upcoming year.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and a Support Specialist at OrcsWeb, a hosted server company providing managed hosting solutions
WPI PHP Manager installation failure
I have noticed a few questions on forums.iis.net related to being unable to install PHP Manager using the Web Platform Installer. The WPI logs are usually pretty good at showing why an install failed. In this instance, the following was listed:
ERROR : [01/24/2014 09:37:49:386] [VsdLaunchConditions ]: Custom Action failed with code: ‘1603’
INFO : [01/24/2014 09:37:49:386] [VsdLaunchConditions ]: Custom Action completed with return code: ‘1603’
This return code points to an issue with the MSI installer and I was unable to locate anything even remotely associated with what was causing the failure after multiple web searches. In the same forums thread, another user mentioned performing a manual install of PHP Manager on the same server and received a much more descriptive and helpful error. The install failed stating that .Net Framework v2.0 is required.
The .Net framework versions are not enabled by default on the newer server operating systems. To remedy this issue, use the Add Roles and Features option within Server Manager. Add the .NET Framework 3.5 Features (and any required dependencies). Once you have completed this install, you will be able to successfully install PHP Manager using WPI.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and a Support Specialist at OrcsWeb, a hosted server company providing managed hosting solutions
Configuring IIS to use a UNC share as the root of a website or application
My team was recently working on a configuration for an OrcsWeb hosting client with a very large web root folder in order to provide a load balanced web redundant solution. The clients users are able to upload files via the web interface so the data has to be synchronized rather than just a one-way replication. Due to data and HDD size constraints, DFS-R is not a viable option. As a workaround, we decided to configure a UNC share and point both nodes to the same location. We created the same share on both servers so that we could use robocopy to sync data to the standby share. This will require manual administrative work in the event of a necessary failover to the standby UNC share but it provides the data redundancy that the client desires.
Since this is a process we have done many times, we were already aware of the need to grant access to the share using the caspol command. If you need to do this in your configuration, here is a blog post that explains the process and steps to implement it. After configuring the share, the website was updated to point the the UNC share and testing began. When testing from the server that the share was hosted on, everything worked as expected. We then tested from the second server and quickly received the following error:
Exception Details: System.Security.SecurityException: Request for the permission of type ‘System.Web.AspNetHostingPermission, System, Version=2.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089′ failed.
To verify that the appropriate permissions were available, we created a test website and pointed to a new web root UNC share that only contained a default.aspx file. We ran the caspol command to grant access remotely and were able to browse the new site from both servers.
We used procmon.exe to determine if there were any access denied errors being logged to try to narrow down the root cause of the failure. No errors were reported. I then remembered reading about the changes that were implemented with the AppPoolIdentity in IIS7; specifically that the Application Pool identity uses the machine account to access network resources. Even though we were using a domain based user account for the application pool, we decided to add the computer account with read permissions to the share. Voila, we were then able to browse the site successfully from either web node. I can not explain why this was necessary but it resolved the error we were encountering. Hopefully this will save you some time in troubleshooting UNC share access issues with IIS if you decide to implement this configuration.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and a Support Specialist at OrcsWeb, a hosted server company providing managed hosting solutions
IIS Troubleshooting
Recently I wrote a troubleshooting blog for work that uses a couple built-in Windows/IIS features and finally Debug Diagnostics to determine root cause of high CPU usage for a website. The referenced utilities were the Worker Processes feature of IIS, Resource Monitor, and DebugDiag. By using these 3 free utilities, you can diagnose long running pages/queries, determine if the process is waiting on a response from IIS or SQL or another external call, and possibly even find the resolution for the problem by taking a process dump and evaluating it. Check out the full blog post here.
Terri is a Microsoft MVP (ASP .NET/IIS), an MCSA: Windows Server 2012, and a Support Specialist at OrcsWeb, a hosted server company providing managed hosting solutions


